Google has released an emergency security update for its Chrome browser to address CVE-2025-13223, a high-severity type...
Enterprise Security
Google has announced a significant policy change for the Google Play Store, targeting Android applications that cause...
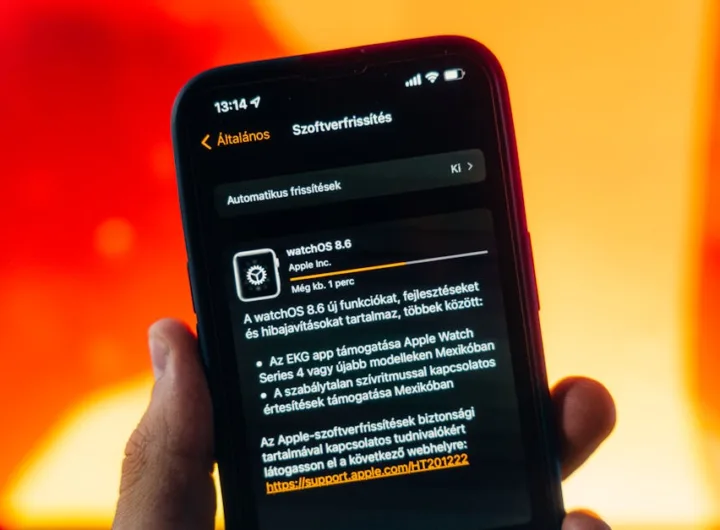
In a significant development for identity verification systems, Apple has joined Google in enabling travelers to store...
Microsoft is rolling out a new security feature for Teams Premium users designed to prevent unauthorized screenshots...
The rapid integration of artificial intelligence into critical sectors has created a complex legal landscape where responsibility...
Microsoft has fundamentally altered the authentication landscape on Windows 11 by enabling native, system-level support for third-party...
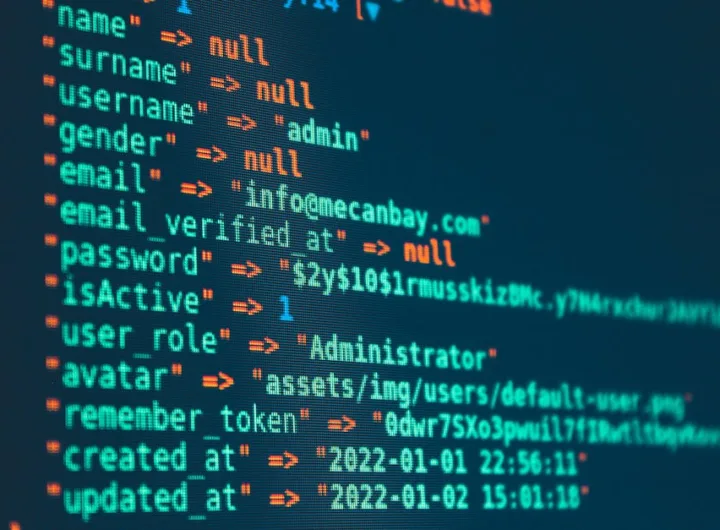
Many organizations continue to struggle with the fundamental security task of patching software vulnerabilities quickly enough to...
Mozilla has released Firefox 145, introducing a significant upgrade to its anti-fingerprinting technology that substantially reduces the...
NAKIVO Inc. has launched Backup & Replication v11.1, a substantial update that significantly expands the platform’s disaster...
A significant Microsoft 365 outage is actively preventing users from accessing critical services, including Microsoft Teams and...
Microsoft has initiated a significant change in Exchange Online by enabling threshold-based auto-archiving by default for all...
Docker has fundamentally changed its approach to container security by making its Hardened Images catalog available through...
Security teams are currently inundated with threat intelligence, creating a significant gap between the discovery of new...
Google has formally launched a dedicated AI Vulnerability Reward Program (AI VRP), creating a structured channel for...
The U.S. Supreme Court has denied Google’s emergency request to block a major antitrust injunction, compelling significant...
The Redis security team has issued patches for a critical, maximum-severity vulnerability that enables authenticated attackers to...
Signal has completed a significant cryptographic upgrade to its protocol with the introduction of the Sparse Post-Quantum...
Amazon’s Ring has announced a significant shift in its home security product line, integrating facial recognition directly...
On October 3, 2025, Apple removed the ICEBlock application and similar software from its App Store, a...
Google has officially launched a feature enabling Gmail users with Client-Side Encryption (CSE) to send end-to-end encrypted...