Active Directory penetration testing remains a cornerstone of enterprise security assessments, with tools like Netexec providing robust capabilities for identifying vulnerabilities and simulating attacker behaviors. This guide examines Netexec’s role in security testing, focusing on reconnaissance, privilege escalation detection, and its alignment with MITRE ATT&CK frameworks—without endorsing exploitation techniques lacking documented proof of concept.
Netexec in Modern Security Assessments
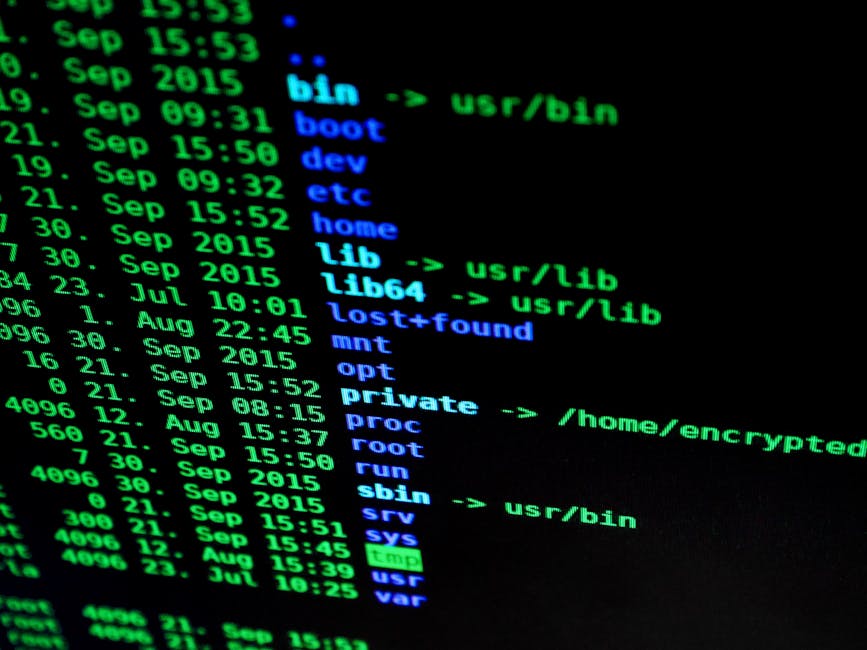
Netexec (formerly CrackMapExec) has emerged as a preferred tool for security professionals conducting Active Directory assessments. Its Python-based architecture supports protocols like LDAP, SMB, and WinRM, enabling comprehensive testing while maintaining operational flexibility. The tool’s command structure follows a logical pattern:
nxc ldap <target> -u <username> -p <password> <options>Key parameters include target specification (domain controllers or endpoints), credential sets for authenticated testing, and module selection for specific attack simulations. Security teams leverage these capabilities to identify configuration weaknesses while maintaining compliance with authorized testing boundaries.
Reconnaissance Techniques
Netexec facilitates several discovery operations that map to MITRE ATT&CK techniques:
Account Enumeration
The tool’s user discovery module helps identify active accounts and group memberships, supporting security audits for stale credentials or inappropriate privileges. Example commands retrieve domain user lists while filtering for enabled accounts—a capability useful for both offensive and defensive security operations.
Kerberos Protocol Analysis
Netexec can identify accounts vulnerable to Kerberos-based attacks, such as those missing pre-authentication requirements. These checks help organizations remediate configuration issues before malicious actors exploit them. The tool outputs hashes in formats compatible with standard cracking tools, though actual cracking falls outside authorized testing without explicit permission.
Privilege Escalation Detection
Netexec’s privilege escalation modules help identify dangerous permission configurations:
DACL Analysis
The tool scans for excessive permissions like WriteDacl or GenericAll rights that could enable privilege escalation. These checks help organizations validate their access control implementations against least privilege principles.
LAPS Assessment
For environments using Microsoft’s Local Administrator Password Solution, Netexec can verify proper implementation and identify potential exposure points for these critical credentials.
Operational Security Considerations
When used properly, Netexec supports several security functions:
- Red Teams: Simulate attacker workflows while maintaining operational security
- Blue Teams: Validate detection capabilities and audit AD configurations
- Security Leadership: Quantify risk exposure from common AD vulnerabilities
Recommended mitigations include enforcing Kerberos pre-authentication, regular permission audits, and monitoring for unusual account activity patterns.
Conclusion
Netexec provides security teams with a powerful toolkit for Active Directory assessments when used responsibly. Its integration with established frameworks like MITRE ATT&CK enables structured testing methodologies that align with modern security practices. Organizations should incorporate these capabilities into their broader security testing programs while maintaining appropriate authorization boundaries.
References
- NetExec Documentation – Official tool documentation
- MITRE ATT&CK Framework – Tactics and techniques reference
- Microsoft AD Security Guidelines – Hardening recommendations






